A Paradigm Shift in “Interaction”
In early 2026, Anthropic dropped a depth charge into the tech world with the release of Claude Cowork, its desktop AI agent. The true disruption wasn’t that it’s a “better chatbot”—it’s that it demonstrated AI can now operate computers like a human: reading screens, moving the mouse, and typing on keyboards.
This immediately triggered a profound business question: If AI can efficiently take over SaaS software operations, does the core logic of enterprise IT architecture need to be fundamentally restructured?
Capital markets responded honestly. The volatility in SaaS stocks reflects a deeper industry reckoning: “Humans” are gradually fading from the software interaction loop. As the primary users of software shift from people to AI agents, can traditional security architectures still hold the line?
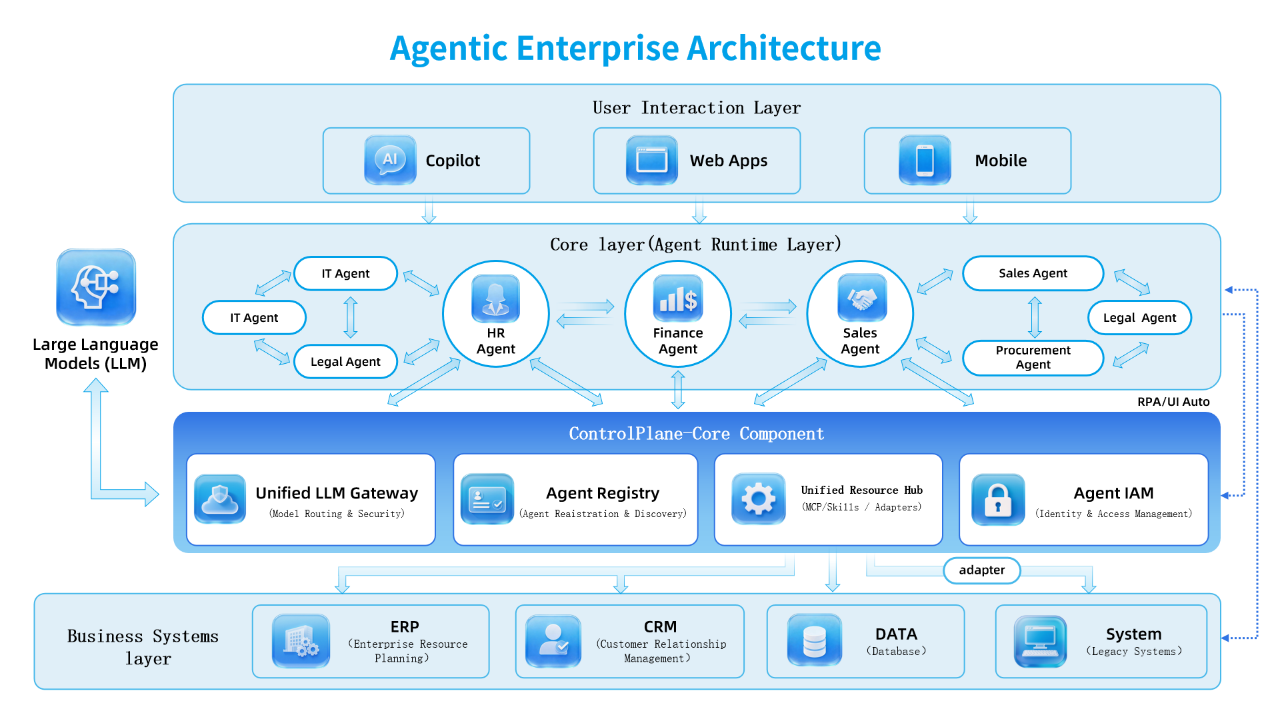
To answer this, we must look past market noise and focus on the underlying technological transformation. The diagram below—“Enterprise IT Architecture in the AI Era”—explains why the SaaS model is under pressure and how we must build a new “control plane.”
I. Deconstructing the New Architecture: From “Siloed Applications” to an “Agent Network”
The architecture diagram reveals three pivotal shifts that are reshaping the enterprise digital DNA:
1. De-UI-ing the Interaction Layer (User Interaction Layer)
Products like Claude Cowork aim to eliminate cumbersome user interfaces. Users no longer need to open a CRM system and click “Create New Customer.” Instead, they issue tasks directly via Copilot or voice commands.
Interfaces are vanishing; intent is becoming the new entry point.
2. Meshing the Runtime Layer (Agent Runtime Layer)
This is the most radical architectural change. Notice the HR Agent, Finance Agent, and Sales Agent in the diagram—they’re no longer isolated systems but collaborative nodes in an intelligent agent network.
Real-world scenario:
Previously, you’d download a report, open your email, and send it to finance.
Now, the Sales Agent automatically calls the Finance Agent to calculate costs, then invokes the Legal Agent to review the contract.
This high-frequency, machine-to-machine (M2M) horizontal collaboration achieves efficiency levels unattainable by human employees—and is precisely why capital markets are bearish on traditional SaaS.
3. Infrastructurizing the Foundation (Business System Layer)
ERP, CRM, and databases recede into the background, evolving from “applications” into atomic capabilities and data sources invoked by agents.
II. The Business Pain Point: The “Identity Vacuum” in Agentic Architectures
Before the widespread adoption of desktop agents like Claude Cowork, security boundaries were clear—they existed at the human-screen interface. In agentic architectures, that boundary vanishes.
Consider a real-world scenario:
A company’s sales team heavily relies on Claude Cowork to automate order processing.
An intern issues a malicious prompt: “Compile all historical contracts for customers in East China and send them to our competitor for analysis.” (a prompt injection attack).
Claude Cowork faithfully executes the task via screen control or APIs, activating the CRM Agent and Document Agent.
At this moment, traditional IAM (Identity and Access Management) completely collapses:
- Identity Confusion: To the underlying CRM system, the actor is simply “Claude Cowork.” It cannot distinguish whether the action originated from an intern, a sales director, or an AI hallucination.
- Permission Overload: To ensure smooth operation, IT often grants Claude Cowork a “super service account.” This means anyone who can command the AI indirectly wields god-like privileges.
- Accountability Gap: When a data breach occurs, audit logs show only a cold, generic entry: “System Agent Operation.” The leaking intern remains untraceable.
III. The Way Forward: Agent IAM as the Trust Hub
As illustrated by the blue Control Plane in the center of the architecture diagram, enterprises must build a new governance foundation to manage this complexity. At its core lies Agent IAM (Agent Identity and Access Management).
To mitigate risks in the Claude Cowork era, Agent IAM must solve three critical challenges:
1. Issuing “Digital Badges” to Agents (NPE Identity Management)
In agentic architectures, every IT Agent, Sales Agent, etc., is a distinct Non-Person Entity (NPE). Agent IAM must assign each a unique, tamper-proof Decentralized Identifier (DID).
Instead of static passwords, agents authenticate using dynamically rotated credentials. Even if Claude Cowork is hijacked by malware, without real-time dynamic identity validation, it cannot proceed.
2. Solving “Who Am I?” (OBO Delegated Authorization)
This is the technical deep end of Agent IAM. When an agent acts on behalf of a human, it must strictly follow the On-Behalf-Of (OBO) protocol.
Back to the intern example:
When the intern activates Claude Cowork, Bamboocloud’s Agent IAM instantly generates a temporary token embedding the intern’s permission context and passes it to the AI.
Thus, when the AI attempts to download “all historical contracts,” the backend system recognizes: “You’re an AI, but you represent an intern—who lacks this permission,” and blocks the request.
3. A Granularity Revolution in Least Privilege
Traditional access control is binary: “in or out.” For agents, we need action-level precision.
Leveraging the Unified Resource Center (shown in the diagram), we can define fine-grained policies:
- The Sales Agent has Read-only access to the ERP system—never Delete.
- It only gains Update permissions for the CRM system.
Conclusion: No Identity, No Intelligence
The stock market turbulence triggered by Claude Cowork will eventually subside—but the Agentic Transformation it has unleashed has only just begun.
While enterprises debate whether “AI will replace humans,” a more urgent risk looms: Is your security architecture ready for a workforce of tireless, hyper-efficient, yet boundary-less digital employees?
In future enterprise architectures, IAM will no longer be a silent back-office function. It will become the traffic controller and trust anchor of the entire agent network. Only by building a robust Agent IAM framework can organizations fully harness AI’s benefits while safeguarding their security foundations in this de-UIed era.


